华为防火墙:GRE over IPSec-(ipsec安全策略方式)-(点到点)-(静态路由)
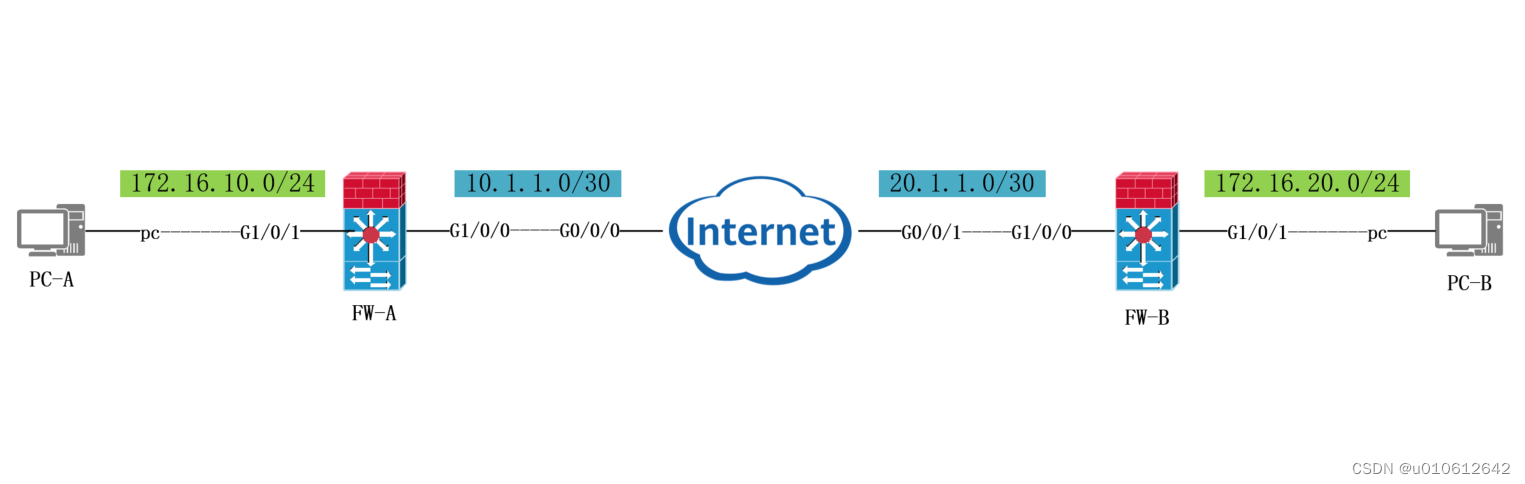
1、Internet上仅配置IP地址
2、FW-A和FW-B之间配置GRE over ipsec tunnel隧道
3、配置静态路由使A-B两个网络互通
防火墙安全策略配置
| 源安全区域 | 目的安全区域 | 源地址 | 目的地址 |
| untrust | local | gre-remote-公网IP | gre-local-公网IP |
| local | untrust | gre-local-公网IP | gre-remote-公网IP |
| trust | tunnel接口所在区域 | reg-local-匹配流量 | gre-remote-匹配流量 |
| tunnel接口所在区域 | trust | gre-remote-匹配流量 | gre-local-匹配流量 |
ACL配置A-B两端的公网地址(GRE数据流)
---------------------------------------------------------------------------------------------------------------------------------
FW-A配置
基本配置
[FW-A]int GigabitEthernet 1/0/0
[FW-A-GigabitEthernet1/0/0]ip add 10.1.1.1 30
[FW-A-GigabitEthernet1/0/0]q
[FW-A]int GigabitEthernet 1/0/1
[FW-A-GigabitEthernet1/0/1]ip add 172.16.10.254 24
[FW-A-GigabitEthernet1/0/1]q
[FW-A]firewall zone trust
[FW-A-zone-trust]add interface GigabitEthernet 1/0/1
[FW-A-zone-trust]q
[FW-A]firewall zone untrust
[FW-A-zone-untrust]add interface g1/0/0
[FW-A-zone-untrust]q
配置gre tunnel
[FW-A]interface Tunnel 1
[FW-A-Tunnel1] description to_network-b
[FW-A-Tunnel1] ip address 1.1.1.1 24
[FW-A-Tunnel1] tunnel-protocol gre
[FW-A-Tunnel1] source 10.1.1.1
[FW-A-Tunnel1] destination 20.1.1.1
[FW-A-Tunnel1] gre key cipher 123456
[FW-A-Tunnel1] quit
[FW-A]firewall zone name gre
[FW-A-zone-gre] set priority 10
[FW-A-zone-gre] add interface Tunnel1
[FW-A-zone-gre] quit
配置路由
[FW-A]ip route-static 0.0.0.0 0.0.0.0 10.1.1.2
[FW-A]ip route-static 172.16.20.0 255.255.255.0 Tunnel 1
配置ipsec
ACL配置A-B两端的公网地址(GRE数据流)
[FW-A]acl number 3000
[FW-A-acl-adv-3000] rule 5 permit ip source 10.1.1.1 0 destination 20.1.1.1 0
[FW-A-acl-adv-3000]quit
[FW-A]ike proposal 10
[FW-A-ike-proposal-10] encryption-algorithm aes-256
[FW-A-ike-proposal-10] dh group18
[FW-A-ike-proposal-10] authentication-algorithm sha2-512
[FW-A-ike-proposal-10] authentication-method pre-share
[FW-A-ike-proposal-10] integrity-algorithm hmac-sha2-256
[FW-A-ike-proposal-10] prf hmac-sha2-256
[FW-A-ike-proposal-10] quit
[FW-A]ike peer fw
[FW-A-ike-peer-fw] exchange-mode main
[FW-A-ike-peer-fw] pre-shared-key huawei
[FW-A-ike-peer-fw] ike-proposal 10
[FW-A-ike-peer-fw] remote-address 20.1.1.1
[FW-A-ike-peer-fw] quit
[FW-A]ipsec proposal 10
[FW-A-ipsec-proposal-10] transform esp
[FW-A-ipsec-proposal-10] encapsulation-mode tunnel
[FW-A-ipsec-proposal-10] esp authentication-algorithm sha2-512
[FW-A-ipsec-proposal-10] esp encryption-algorithm aes-256
[FW-A-ipsec-proposal-10] quit
[FW-A]ipsec policy ipsec 1 isakmp
[FW-A-ipsec-policy-isakmp-ipsec-1] security acl 3000
[FW-A-ipsec-policy-isakmp-ipsec-1] ike-peer fw
[FW-A-ipsec-policy-isakmp-ipsec-1] proposal 10
[FW-A-ipsec-policy-isakmp-ipsec-1] quit
[FW-A]interface GigabitEthernet1/0/0
[FW-A-GigabitEthernet1/0/0] ipsec policy ipsec
[FW-A-GigabitEthernet1/0/0] quit
配置安全策略
[FW-A]security-policy
[FW-A-policy-security] rule name local_remote
[FW-A-policy-security-rule-local_remote] source-zone local
[FW-A-policy-security-rule-local_remote] destination-zone untrust
[FW-A-policy-security-rule-local_remote] source-address 10.1.1.1 0.0.0.0
[FW-A-policy-security-rule-local_remote] destination-address 20.1.1.1 0.0.0.0
[FW-A-policy-security-rule-local_remote] action permit
[FW-A-policy-security-rule-local_remote] quit
[FW-A-policy-security] rule name remote_local
[FW-A-policy-security-rule-remote_local] source-zone untrust
[FW-A-policy-security-rule-remote_local] destination-zone local
[FW-A-policy-security-rule-remote_local] source-address 20.1.1.1 0.0.0.0
[FW-A-policy-security-rule-remote_local] destination-address 10.1.1.1 0.0.0.0
[FW-A-policy-security-rule-remote_local] action permit
[FW-A-policy-security-rule-remote_local] quit
[FW-A-policy-security] rule name neiwang_a-neiwang_b
[FW-A-policy-security-rule-neiwang_a-neiwang_b] source-zone trust
[FW-A-policy-security-rule-neiwang_a-neiwang_b] destination-zone gre
[FW-A-policy-security-rule-neiwang_a-neiwang_b] source-address 172.16.10.0 mask 255.255.255.0
[FW-A-policy-security-rule-neiwang_a-neiwang_b] destination-address 172.16.20.0 mask 255.255.255.0
[FW-A-policy-security-rule-neiwang_a-neiwang_b] action permit
[FW-A-policy-security-rule-neiwang_a-neiwang_b] quit
[FW-A-policy-security] rule name neiwang_b-neiwang_a
[FW-A-policy-security-rule-neiwang_b-neiwang_a] source-zone gre
[FW-A-policy-security-rule-neiwang_b-neiwang_a] destination-zone trust
[FW-A-policy-security-rule-neiwang_b-neiwang_a] source-address 172.16.20.0 mask 255.255.255.0
[FW-A-policy-security-rule-neiwang_b-neiwang_a] destination-address 172.16.10.0 mask 255.255.255.0
[FW-A-policy-security-rule-neiwang_b-neiwang_a] action permit
[FW-A-policy-security-rule-neiwang_b-neiwang_a] quit
[FW-A-policy-security]q
FW-B配置
[FW-B]int GigabitEthernet 1/0/0
[FW-B-GigabitEthernet1/0/0]ip add 20.1.1.1 30
[FW-B-GigabitEthernet1/0/0]q
[FW-B]int GigabitEthernet 1/0/1
[FW-B-GigabitEthernet1/0/1]ip add 172.16.20.254 24
[FW-B-GigabitEthernet1/0/1]q
[FW-B]firewall zone trust
[FW-B-zone-trust]add interface GigabitEthernet 1/0/1
[FW-B-zone-trust]q
[FW-B]firewall zone untrust
[FW-B-zone-untrust]add interface g1/0/0
[FW-B-zone-untrust]q
[FW-B]interface Tunnel 1
[FW-B-Tunnel1] description to_network-a
[FW-B-Tunnel1] ip address 1.1.1.2 255.255.255.0
[FW-B-Tunnel1] tunnel-protocol gre
[FW-B-Tunnel1] source 20.1.1.1
[FW-B-Tunnel1] destination 10.1.1.1
[FW-B-Tunnel1] gre key cipher 123456
[FW-B-Tunnel1] quit
[FW-B]ip route-static 0.0.0.0 0.0.0.0 20.1.1.2
[FW-B]ip route-static 172.16.10.0 24 Tunnel 1
[FW-B]firewall zone name gre
[FW-B-zone-gre] set priority 10
[FW-B-zone-gre] add interface Tunnel1
[FW-B-zone-gre] quit
[FW-B]acl number 3000
[FW-B-acl-adv-3000] rule 5 permit ip source 20.1.1.1 0 destination 10.1.1.1 0
[FW-B-acl-adv-3000]quit
[FW-B]ike proposal 10
[FW-B-ike-proposal-10] encryption-algorithm aes-256
[FW-B-ike-proposal-10] dh group18
[FW-B-ike-proposal-10] authentication-algorithm sha2-512
[FW-B-ike-proposal-10] authentication-method pre-share
[FW-B-ike-proposal-10] integrity-algorithm hmac-sha2-256
[FW-B-ike-proposal-10] prf hmac-sha2-256
[FW-B-ike-proposal-10] quit
[FW-B]ike peer fw
[FW-B-ike-peer-fw] exchange-mode main
[FW-B-ike-peer-fw] pre-shared-key huawei
[FW-B-ike-peer-fw] ike-proposal 10
[FW-B-ike-peer-fw] remote-address 10.1.1.1
[FW-B-ike-peer-fw] quit
[FW-B]ipsec proposal 10
[FW-B-ipsec-proposal-10] transform esp
[FW-B-ipsec-proposal-10] encapsulation-mode tunnel
[FW-B-ipsec-proposal-10] esp authentication-algorithm sha2-512
[FW-B-ipsec-proposal-10] esp encryption-algorithm aes-256
[FW-B-ipsec-proposal-10] quit
[FW-B]ipsec policy ipsec 1 isakmp
[FW-B-ipsec-policy-isakmp-ipsec-1] security acl 3000
[FW-B-ipsec-policy-isakmp-ipsec-1] ike-peer fw
[FW-B-ipsec-policy-isakmp-ipsec-1]
[FW-B-ipsec-policy-isakmp-ipsec-1] proposal 10
[FW-B-ipsec-policy-isakmp-ipsec-1] quit
[FW-B]interface GigabitEthernet1/0/0
[FW-B-GigabitEthernet1/0/0] ipsec policy ipsec
[FW-B-GigabitEthernet1/0/0] quit
[FW-B]security-policy
[FW-B-policy-security] rule name local_remote
[FW-B-policy-security-rule-local_remote] source-zone local
[FW-B-policy-security-rule-local_remote] destination-zone untrust
[FW-B-policy-security-rule-local_remote] source-address 20.1.1.1 0.0.0.0
[FW-B-policy-security-rule-local_remote] destination-address 10.1.1.1 0.0.0.0
[FW-B-policy-security-rule-local_remote] action permit
[FW-B-policy-security-rule-local_remote] q
[FW-B-policy-security] rule name remote_local
[FW-B-policy-security-rule-remote_local] source-zone untrust
[FW-B-policy-security-rule-remote_local] destination-zone local
[FW-B-policy-security-rule-remote_local] source-address 10.1.1.1 0.0.0.0
[FW-B-policy-security-rule-remote_local] destination-address 20.1.1.1 0.0.0.0
[FW-B-policy-security-rule-remote_local] action permit
[FW-B-policy-security-rule-remote_local] q
[FW-B-policy-security]rule name neiwang_b-neiwang_ac
[FW-B-policy-security-rule-neiwang_b-neiwang_ac] source-zone trust
[FW-B-policy-security-rule-neiwang_b-neiwang_ac] destination-zone gre
[FW-B-policy-security-rule-neiwang_b-neiwang_ac] source-address 172.16.20.0 mask 255.255.255.0
[FW-B-policy-security-rule-neiwang_b-neiwang_ac] destination-address 172.16.10.0 mask 255.255.255.0
[FW-B-policy-security-rule-neiwang_b-neiwang_ac] action permit
[FW-B-policy-security-rule-neiwang_b-neiwang_ac] q
[FW-B-policy-security] rule name neiwang_ac-neiwang_b
[FW-B-policy-security-rule-neiwang_ac-neiwang_b] source-zone gre
[FW-B-policy-security-rule-neiwang_ac-neiwang_b] destination-zone trust
[FW-B-policy-security-rule-neiwang_ac-neiwang_b] source-address 172.16.10.0 mask 255.255.255.0
[FW-B-policy-security-rule-neiwang_ac-neiwang_b] destination-address 172.16.20.0 mask 255.255.255.0
[FW-B-policy-security-rule-neiwang_ac-neiwang_b] action permit
[FW-B-policy-security-rule-neiwang_ac-neiwang_b] q
[FW-B-policy-security]q
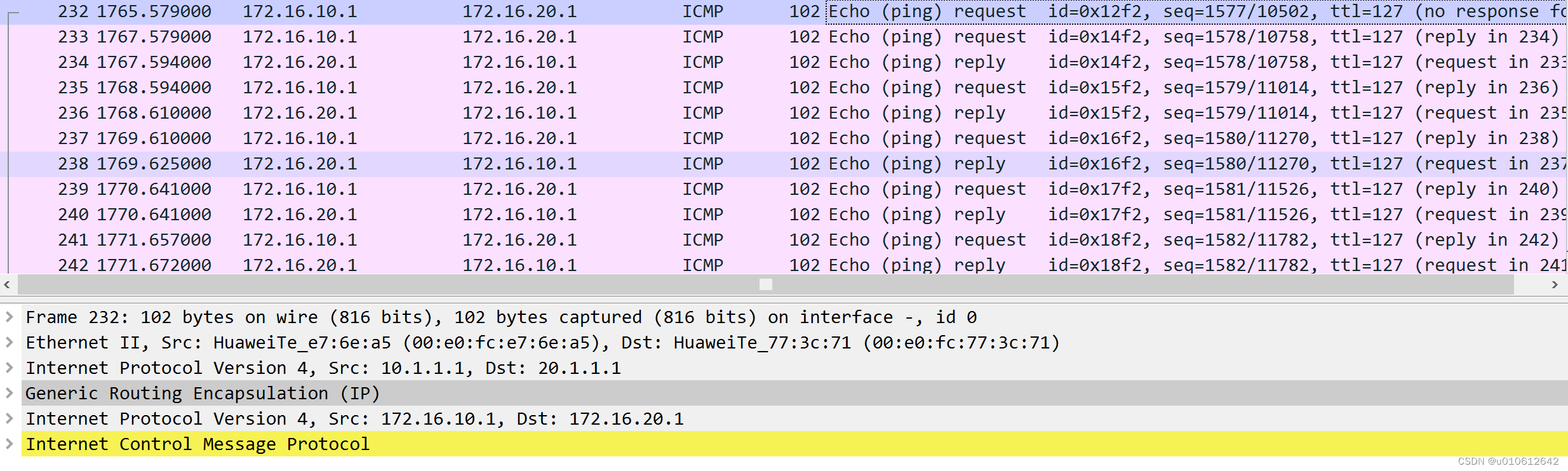
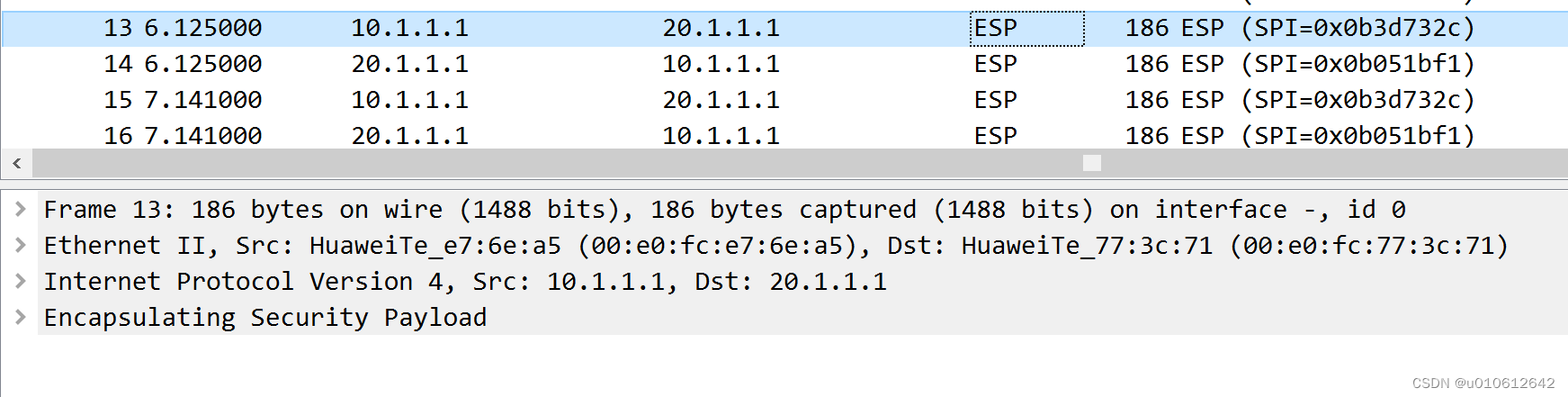
抓包验证
普通gre tunnel抓取到的数据包 没有加密
Gre over ipsec 抓取到的数据包 经过加密
华为OD机试题本篇题目:明明的随机数题目输入描述输出描述:示例1输入输出说明代码编写思路最近更新的博客华为od2023|什么是华为od,od薪资待遇,od机试题清单华为OD机试真题大全,用Python解华为机试题|机试宝典【华为OD机试】全流程解析+经验分享,题型分享,防作弊指南华为o
system-view进入系统视图quit退到系统视图sysname交换机命名vlan20创建vlan(进入vlan20)displayvlan显示vlanundovlan20删除vlan20displayvlan20显示vlan里的端口20Interfacee1/0/24进入端口24portlink-typeaccessvlan20把当前端口放入vlan20undoporte1/0/10删除当前VLAN端口10displaycurrent-configuration显示当前配置02配置交换机支持TELNETinterfacevlan1进入VLAN1ipaddress192.168.3.100
所有题目均有五种语言实现。C实现目录、C++实现目录、Python实现目录、Java实现目录、JavaScript实现目录题目n行m列的矩阵,每个位置上有一个元素你可以上下左右行走,代价是前后两个位置元素值差的绝对值.另外,你最多可以使用一次传送阵(只能从一个数跳到另外一个相同的数)求从走上角走到右下角最少需要多少时间。输入描述:第一行两个整数n,m,分别代表矩阵的行和列。后面n行,每行m个整数,分别代表矩阵中的元素。输出描述:一个整数,表示最少需要多少时间。
西安华为OD面试体验开始投简历技术面试进展工作进展开始投简历去年一整年一直在考研和工作之间纠结,感觉自己的状态好像当时的疫情一样差劲。之前刚毕业的时候投了个大厂的简历,结果一面写算法的时候太拉跨了,虽然知道时dfs但是代码熟练度不够,放在平时给足时间自己可以调试通过,但是熟练度不够那面试当时就写不出来被刷了。说真的算法学到后期我感觉最重要的是熟练度和背板子(对于我这种普通玩家来说),面试题如果一上来短时间内想不出思路就完蛋了。然后由于当时找的工作不是很理想就又想考研了。但是考研是有风险的,我自我感觉自己可能冲不上那个学校,而找工作一个没成可以继续找嘛。本着抱着试试看的态度在boss上投了简历,
目录一、安装包链接二、安装详细步骤1.安装Wireshark和WinPcap2.安装OracleVMVirtualBox3.安装ensp三、安装后注册四、启动路由器出现40错误怎么解决一、安装包链接二、安装详细步骤链接:https://pan.baidu.com/s/1QbUUYMOMIV2oeIKHWP1SpA?pwd=xftx提取码:xftx1.安装Wireshark和WinPcap找到Wireshark安装包所在文件夹,双击它,按照以下步骤安装。2.安装OracleVMVirtualBox找到OracleVMVirtualBox安装包所在文件夹,双击它,按照以下步骤安装。注:可自定义安装
近日,上海证券交易所科创板披露的信息显示,嘉兴中润光学科技股份有限公司(下称“中润光学”)获得上市委会议通过。这意味着,中润光学的上市之路获得实质性进展,接下来将提交注册。据贝多财经了解,中润光学的招股书于2022年5月20日获得科创板受理,5个月后便获得上市委会议通过,进度不可谓不快。本次冲刺科创板上市,中润光学拟募资4.05亿元,计划用于高端光学镜头智能制造项目、高端光学镜头研发中心升级项目等。天眼查信息显示,中润光学成立于2012年8月,是一家以从事非金属矿物制品业为主的企业。当前,该公司的注册资本为6600万元,法定代表人为张平华。穿透股权可知,张平华也是该公司的实际控制人。据招股书介
三大公有云厂商,香港地区主机测评一、ping时延比对(厦门电信本地测试):Ping时延测试腾讯云阿里云华为云延迟率最低时延44ms,最高72ms,平均46ms47.242段:最低时延59ms,最高204ms,平均107ms最低时延45ms,最高93ms,平均47ms丢包率丢包率小有的ip段丢包率较大每个段都会有概率丢包阿里云:47.242段:最低时延59ms,最高204ms,平均107ms,有的ip段丢包率较大8.210段:最低时延64ms,最高232ms,平均119ms,丢包率较好腾讯云:最低时延44ms,最高72ms,平均46ms,丢包率小华为云:最低时延45ms,最高93ms,平均47m
WAF可以对网站进行扫描,识别API漏洞。API安全如何设置API安全_Web应用防火墙-阿里云帮助中心API安全如何划分API业务用途?登录认证手机验证码认证数据保存数据查询数据导出数据分享数据更新数据删除数据增加下线注销信息发送信息认证邮件信息发送邮箱验证码认证账号密码认证账号注册API安全支持检测哪些敏感数据?敏感数据级别敏感数据类型非敏感数据(N)不涉及。特级敏感数据(L0)与一级敏感数据(L1)或二级敏感数据(L2)相同。单次响应中一级敏感数据(L1)较多时,升级为特级敏感数据(L0)。单次响应中二级敏感数据(L2)较多时,升级为一级敏感数据(L1)或特级敏感数据(L0)。一级敏感数
华为认证分等级的,相当于初中高三个等级,当然高级是比较难考的,也是含金量最高的。我就慢慢给你介绍一下。1.了解华为认证华为认证网络工程师是由华为公司认证与采购部推出的独立认证体系,与之前的华为认证不同,简称HCIA。同时华为认证是华为技术有限公司凭借多年信息通信技术人才培养经验,以及对行业发展的理解,以层次化的职业技术认证为指引,推出的覆盖IP、IT、CT以及ICT融合技术领域的认证体系,是ICT全技术领域认证体系。2.怎么考取华为认证网络工程师?要考取华为认证网络工程师必须选择最近的Prometric授权考试中心APTC报名并参加GB0-190的考试,考试通过后,以获得由华为统一签发的“华
一、网络环境及TOP1.1R1相当于内网的一台PC, IP:192.168.1.10 网关为 192.168.1.254[R1]iproute-static0.0.0.00192.168.1.254#R1配置默认路由(网关)1.2R2为出口路由器,分别连接内网R1及外网R31)R2 内网接口IP:192.168.1.2542)R2外网接口IP:100.1.1.102)R2NAT地址为:100.1.1.11-100.1.1.14二、静态NAT配置1.1静态NAT(一对一双向)R2配置静态NAT,将公网IP100.1.1.11映射到内网R1 192.168.1.10[R2]intg0/0/1[R2