AccessKey 保存至本地
TF_VAR 开头,这样就被 terraform 在读取环境变量时就认为是他自己的环境变量虽然也可以写在配置文件中明文保存,但是强烈不建议这样用,一旦配置文件泄露,便有非常大的风险。# 第一种方式,需要去掉 main.tf 中的变量,直接全空即可,此变量是官方默认提供变量,不需要加 TF_VAR
export ALICLOUD_ACCESS_KEY="LTA**************<strong>"
export ALICLOUD_SECRET_KEY="Hp</strong>**************"
export ALICLOUD_REGION="cn-beijing"# 第二种方式,下边定义阿里云 provider 用的是第二种
export TF_VAR_access_key="LTA**************<strong>"
export TF_VAR_secret_key="Hp</strong>**************"
export TF_VAR_region="cn-beijing"# versions.tf
// 定义 terraform 的 版本信息
terraform {
required_version = ">= 1.1.0"
required_providers {
alicloud = {
source = "aliyun/alicloud"
version = "1.162.0"
}
}
}# variables.tf
// 定义的变量会从环境变量中取值
// 分别对应 ALICLOUD_ACCESS_KEY, ALICLOUD_SECRET_KEY, ALICLOUD_REGION
variable "access_key" {
type = string
}
variable "secret_key" {
type = string
}
variable "region" {
type = string
}# main.tf
// 阿里云登录信息,采用的是环境变量
provider "alicloud" {
# Configuration options
access_key = var.access_key
secret_key = var.secret_key
region = var.region
}# alicloud_vpc.tf
// 创建 VPC 专有网络
resource "alicloud_vpc" "vpc" {
vpc_name = "tf_test_foo"
cidr_block = "172.96.0.0/12"
}
// 创建 Vswitch 交换机
resource "alicloud_vswitch" "vsw" {
vpc_id = alicloud_vpc.vpc.id
cidr_block = "172.96.0.0/21"
zone_id = "cn-beijing-b"
}# alicloud_security_group.tf
// 创建 安全组 group
resource "alicloud_security_group" "group" {
name = "demo-group"
vpc_id = alicloud_vpc.vpc.id
security_group_type = "normal"
}
// 定义安全组规则,放开 22 端口
resource "alicloud_security_group_rule" "allow_22_tcp" {
type = "ingress"
ip_protocol = "tcp"
nic_type = "intranet"
policy = "accept"
port_range = "22/22"
priority = 1
security_group_id = alicloud_security_group.group.id
cidr_ip = "0.0.0.0/0"
}# 相关文件的目录结构
.
├── alicloud_security_group.tf
├── alicloud_vpc.tf
├── main.tf
├── variables.tf
└── versions.tf
0 directories, 5 filesterraform fmtterraform init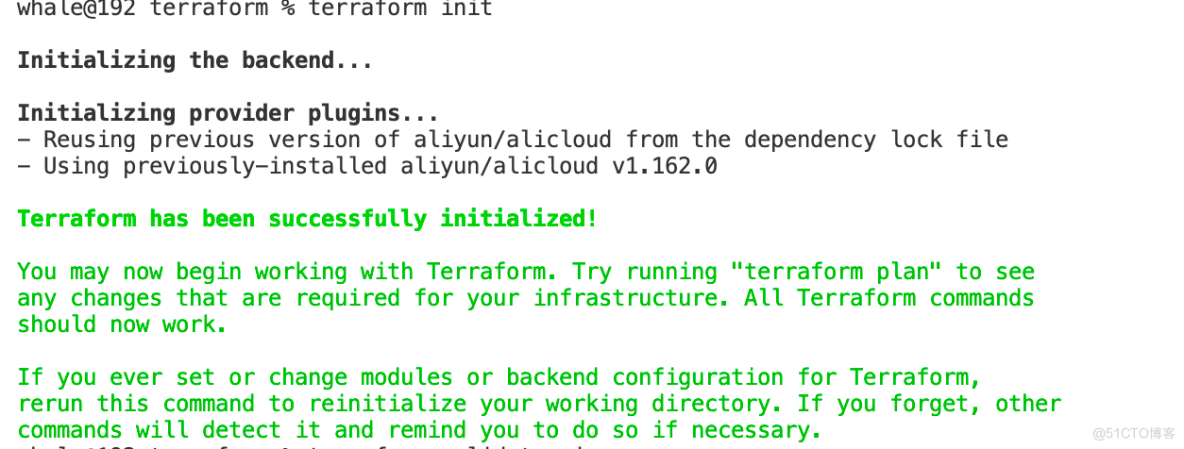 init 的操作会把相关包下载到本地,此步骤时间略长
init 的操作会把相关包下载到本地,此步骤时间略长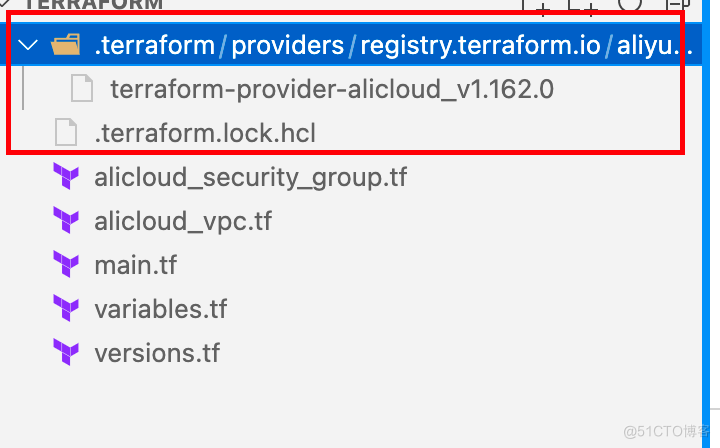
terraform validate -json
# 输出如下结果
{
"format_version": "1.0",
"valid": true,
"error_count": 0,
"warning_count": 0,
"diagnostics": []
}~# terraform plan
Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with the following symbols:
+ create
Terraform will perform the following actions:
# alicloud_security_group.group will be created
+ resource "alicloud_security_group" "group" {
+ id = (known after apply)
+ inner_access = (known after apply)
+ inner_access_policy = (known after apply)
+ name = "demo-group"
+ security_group_type = "normal"
+ vpc_id = (known after apply)
}
# alicloud_security_group_rule.allow_22_tcp will be created
+ resource "alicloud_security_group_rule" "allow_22_tcp" {
+ cidr_ip = "0.0.0.0/0"
+ id = (known after apply)
+ ip_protocol = "tcp"
+ nic_type = "internet"
+ policy = "accept"
+ port_range = "22/22"
+ prefix_list_id = (known after apply)
+ priority = 1
+ security_group_id = (known after apply)
+ type = "ingress"
}
# alicloud_vpc.vpc will be created
+ resource "alicloud_vpc" "vpc" {
+ cidr_block = "172.96.0.0/12"
+ id = (known after apply)
+ ipv6_cidr_block = (known after apply)
+ name = (known after apply)
+ resource_group_id = (known after apply)
+ route_table_id = (known after apply)
+ router_id = (known after apply)
+ router_table_id = (known after apply)
+ status = (known after apply)
+ vpc_name = "tf_test_foo"
}
# alicloud_vswitch.vsw will be created
+ resource "alicloud_vswitch" "vsw" {
+ availability_zone = (known after apply)
+ cidr_block = "172.96.0.0/21"
+ id = (known after apply)
+ name = (known after apply)
+ status = (known after apply)
+ vpc_id = (known after apply)
+ vswitch_name = (known after apply)
+ zone_id = "cn-beijing-b"
}
Plan: 4 to add, 0 to change, 0 to destroy.
────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
Note: You didn't use the -out option to save this plan, so Terraform can't guarantee to take exactly these actions if you run "terraform
apply" now.terraform apply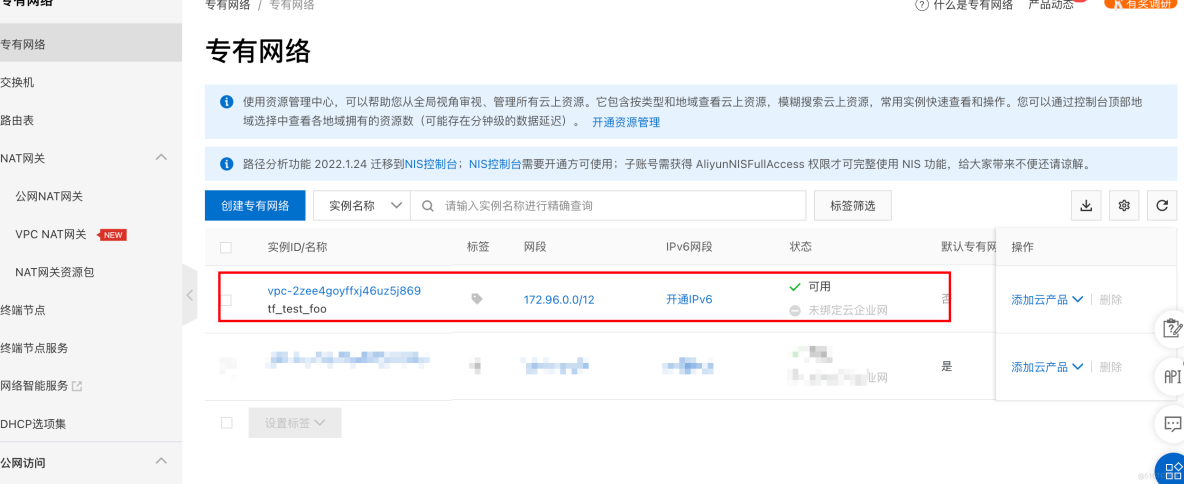 vswitch 验证
vswitch 验证 安全组验证
安全组验证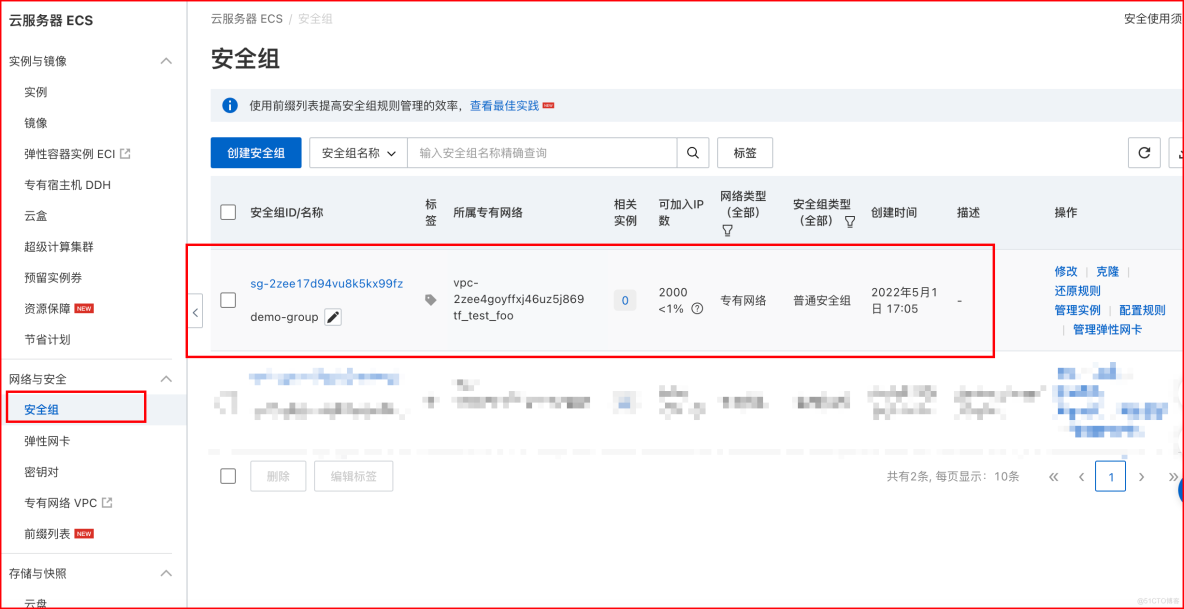

~# terraform show
# alicloud_security_group.group:
resource "alicloud_security_group" "group" {
id = "sg-2zee17d94vu8k5kx99fz"
inner_access = true
inner_access_policy = "Accept"
name = "demo-group"
security_group_type = "normal"
tags = {}
vpc_id = "vpc-2zee4goyffxj46uz5j869"
}
# alicloud_security_group_rule.allow_22_tcp:
resource "alicloud_security_group_rule" "allow_22_tcp" {
cidr_ip = "0.0.0.0/0"
id = "sg-2zee17d94vu8k5kx99fz:ingress:tcp:22/22:intranet:0.0.0.0/0:accept:1"
ip_protocol = "tcp"
nic_type = "intranet"
policy = "accept"
port_range = "22/22"
priority = 1
security_group_id = "sg-2zee17d94vu8k5kx99fz"
type = "ingress"
}
# alicloud_vpc.vpc:
resource "alicloud_vpc" "vpc" {
cidr_block = "172.96.0.0/12"
id = "vpc-2zee4goyffxj46uz5j869"
name = "tf_test_foo"
resource_group_id = "rg-acfmybfthr6yliq"
route_table_id = "vtb-2zeksbc0su4tecdy7j5er"
router_id = "vrt-2ze1lmeuaf424yol3twki"
router_table_id = "vtb-2zeksbc0su4tecdy7j5er"
secondary_cidr_blocks = []
status = "Available"
user_cidrs = []
vpc_name = "tf_test_foo"
}
# alicloud_vswitch.vsw:
resource "alicloud_vswitch" "vsw" {
availability_zone = "cn-beijing-b"
cidr_block = "172.96.0.0/21"
id = "vsw-2zeqb015cd9hogrp6fa4a"
status = "Available"
tags = {}
vpc_id = "vpc-2zee4goyffxj46uz5j869"
zone_id = "cn-beijing-b"
}~# terraform destroy
alicloud_vpc.vpc: Refreshing state... [id=vpc-2zee4goyffxj46uz5j869]
alicloud_security_group.group: Refreshing state... [id=sg-2zee17d94vu8k5kx99fz]
alicloud_vswitch.vsw: Refreshing state... [id=vsw-2zeqb015cd9hogrp6fa4a]
alicloud_security_group_rule.allow_22_tcp: Refreshing state... [id=sg-2zee17d94vu8k5kx99fz:ingress:tcp:22/22:intranet:0.0.0.0/0:accept:1]
Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with the following symbols:
- destroy
Terraform will perform the following actions:
# alicloud_security_group.group will be destroyed
- resource "alicloud_security_group" "group" {
- id = "sg-2zee17d94vu8k5kx99fz" -> null
- inner_access = true -> null
- inner_access_policy = "Accept" -> null
- name = "demo-group" -> null
- security_group_type = "normal" -> null
- tags = {} -> null
- vpc_id = "vpc-2zee4goyffxj46uz5j869" -> null
}
# alicloud_security_group_rule.allow_22_tcp will be destroyed
- resource "alicloud_security_group_rule" "allow_22_tcp" {
- cidr_ip = "0.0.0.0/0" -> null
- id = "sg-2zee17d94vu8k5kx99fz:ingress:tcp:22/22:intranet:0.0.0.0/0:accept:1" -> null
- ip_protocol = "tcp" -> null
- nic_type = "intranet" -> null
- policy = "accept" -> null
- port_range = "22/22" -> null
- priority = 1 -> null
- security_group_id = "sg-2zee17d94vu8k5kx99fz" -> null
- type = "ingress" -> null
}
# alicloud_vpc.vpc will be destroyed
- resource "alicloud_vpc" "vpc" {
- cidr_block = "172.96.0.0/12" -> null
- id = "vpc-2zee4goyffxj46uz5j869" -> null
- name = "tf_test_foo" -> null
- resource_group_id = "rg-acfmybfthr6yliq" -> null
- route_table_id = "vtb-2zeksbc0su4tecdy7j5er" -> null
- router_id = "vrt-2ze1lmeuaf424yol3twki" -> null
- router_table_id = "vtb-2zeksbc0su4tecdy7j5er" -> null
- secondary_cidr_blocks = [] -> null
- status = "Available" -> null
- user_cidrs = [] -> null
- vpc_name = "tf_test_foo" -> null
}
# alicloud_vswitch.vsw will be destroyed
- resource "alicloud_vswitch" "vsw" {
- availability_zone = "cn-beijing-b" -> null
- cidr_block = "172.96.0.0/21" -> null
- id = "vsw-2zeqb015cd9hogrp6fa4a" -> null
- status = "Available" -> null
- tags = {} -> null
- vpc_id = "vpc-2zee4goyffxj46uz5j869" -> null
- zone_id = "cn-beijing-b" -> null
}
Plan: 0 to add, 0 to change, 4 to destroy.
Do you really want to destroy all resources?
Terraform will destroy all your managed infrastructure, as shown above.
There is no undo. Only 'yes' will be accepted to confirm.
Enter a value: yes
alicloud_vswitch.vsw: Destroying... [id=vsw-2zeqb015cd9hogrp6fa4a]
alicloud_security_group_rule.allow_22_tcp: Destroying... [id=sg-2zee17d94vu8k5kx99fz:ingress:tcp:22/22:intranet:0.0.0.0/0:accept:1]
alicloud_security_group_rule.allow_22_tcp: Destruction complete after 7s
alicloud_security_group.group: Destroying... [id=sg-2zee17d94vu8k5kx99fz]
alicloud_security_group.group: Destruction complete after 0s
alicloud_vswitch.vsw: Still destroying... [id=vsw-2zeqb015cd9hogrp6fa4a, 10s elapsed]
alicloud_vswitch.vsw: Destruction complete after 15s
alicloud_vpc.vpc: Destroying... [id=vpc-2zee4goyffxj46uz5j869]
alicloud_vpc.vpc: Destruction complete after 6s
Destroy complete! Resources: 4 destroyed.我正在使用i18n从头开始构建一个多语言网络应用程序,虽然我自己可以处理一大堆yml文件,但我说的语言(非常)有限,最终我想寻求外部帮助帮助。我想知道这里是否有人在使用UI插件/gem(与django上的django-rosetta不同)来处理多个翻译器,其中一些翻译器不愿意或无法处理存储库中的100多个文件,处理语言数据。谢谢&问候,安德拉斯(如果您已经在rubyonrails-talk上遇到了这个问题,我们深表歉意) 最佳答案 有一个rails3branchofthetolkgem在github上。您可以通过在Gemfi
我安装了ruby版本管理器,并将RVM安装的ruby实现设置为默认值,这样'哪个ruby'显示'~/.rvm/ruby-1.8.6-p383/bin/ruby'但是当我在emacs中打开inf-ruby缓冲区时,它使用安装在/usr/bin中的ruby。有没有办法让emacs像shell一样尊重ruby的路径?谢谢! 最佳答案 我创建了一个emacs扩展来将rvm集成到emacs中。如果您有兴趣,可以在这里获取:http://github.com/senny/rvm.el
是否有简单的方法来更改默认ISO格式(yyyy-mm-dd)的ActiveAdmin日期过滤器显示格式? 最佳答案 您可以像这样为日期选择器提供额外的选项,而不是覆盖js:=f.input:my_date,as::datepicker,datepicker_options:{dateFormat:"mm/dd/yy"} 关于ruby-on-rails-事件管理员日期过滤器日期格式自定义,我们在StackOverflow上找到一个类似的问题: https://s
作为新的阿里云用户,您可以50免费试用多种优惠,价值高达1,700美元(或8,500美元)。这将让您了解和体验阿里云平台上提供的一系列产品和服务。如果您以个人身份注册免费试用,您将获得价值1,700美元的优惠。但是,如果您是注册公司,您可以选择企业免费试用,提交基本信息通过企业实名注册验证,即可开始价值$8,500的免费试用!本教程介绍了如何设置您的帐户并使用您的免费试用版。关于免费试用在我们开始此试用之前,您还必须遵守以下条款和条件才能访问您的免费试用:只有在一年内创建的账户才有资格获得阿里云免费试用。通过此免费试用优惠,用户可以免费试用免费试用活动页面上列出的每种产品一次。如果您有多个帐
基础版云数据库RDS的产品系列包括基础版、高可用版、集群版、三节点企业版,本文介绍基础版实例的相关信息。RDS基础版实例也称为单机版实例,只有单个数据库节点,计算与存储分离,性价比超高。说明RDS基础版实例只有一个数据库节点,没有备节点作为热备份,因此当该节点意外宕机或者执行重启实例、变更配置、版本升级等任务时,会出现较长时间的不可用。如果业务对数据库的可用性要求较高,不建议使用基础版实例,可选择其他系列(如高可用版),部分基础版实例也支持升级为高可用版。基础版与高可用版的对比拓扑图如下所示。优势 性能由于不提供备节点,主节点不会因为实时的数据库复制而产生额外的性能开销,因此基础版的性能相对于
我想用这两种语言中的任何一种(最好是ruby)制作一个窗口管理器。老实说,除了我需要加载某种X模块外,我不知道从哪里开始。因此,如果有人有线索,如果您能指出正确的方向,那就太好了。谢谢 最佳答案 XCB,X的下一代API使用XML格式定义X协议(protocol),并使用脚本生成特定语言绑定(bind)。它在概念上与SWIG类似,只是它描述的不是CAPI,而是X协议(protocol)。目前,C和Python存在绑定(bind)。理论上,Ruby端口只是编写一个从XML协议(protocol)定义语言到Ruby的翻译器的问题。生
这是我在ActiveAdmin中的自定义页面ActiveAdmin.register_page"Settings"doaction_itemdolink_to('Importprojects','settings/importprojects')endcontentdopara"Text"endcontrollerdodefimportprojectssystem"rakedataspider:import_projects_ninja"para"OK"endendend我想做的是,当我单击“导入项目”按钮时,我想在Controller中执行rake任务。但是我无法访问该方法。可能是什
我正在寻找用于Rails的优质管理插件。似乎大多数现有的插件/gem(例如“restful_authentication”、“acts_as_authenticated”)都围绕着self注册等展开。但是,我正在寻找一种功能齐全的基于管理/管理角色的解决方案——但不是简单地附加到另一个非基于角色的解决方案。如果我找不到,我想我会自己动手......只是不想重新发明轮子。 最佳答案 RyanBates最近做了两个关于授权的railscast(注意身份验证和授权之间的区别;身份验证检查用户是否如她所说的那样,授权检查用户是否有权访问资源
文章目录一基础定义二创建逻辑卷2-1准备物理设备2-2创建物理卷2-3创建卷组2-4创建逻辑卷2-5创建文件系统并挂载文件三扩展卷组和缩减卷组3-1准备物理设备3-2创建物理卷3-3扩展卷组3-4查看卷组的详细信息以验证3-5缩减卷组四扩展逻辑卷4-1检查卷组是否有可用的空间4-2扩展逻辑卷4-3扩展文件系统五删除逻辑卷5-1备份数据5-2卸载文件系统5-3删除逻辑卷5-4删除卷组5-5删除物理卷六LVM逻辑卷缩容6-1缩容注意事项6-2标准缩容步骤一基础定义LVM,LogicalVolumeManger,逻辑卷管理,Linux磁盘分区管理的一种机制,建立在硬盘和分区上的一个逻辑层,提高磁盘分
我为Devise用户和管理员提供了不同的模型。我也在使用Basecamp风格的子域。除了我需要能够以用户或管理员身份进行身份验证的一些Controller和操作外,一切都运行良好。目前我有authenticate_user!在我的application_controller.rb中设置,对于那些只有管理员才能访问的Controller和操作,我使用skip_before_filter跳过它。不幸的是,我不能简单地指定每个Controller的身份验证要求,因为我仍然需要一些Controller和操作才能被用户或管理员访问。我尝试了一些方法都无济于事。看来,如果我移动authentica